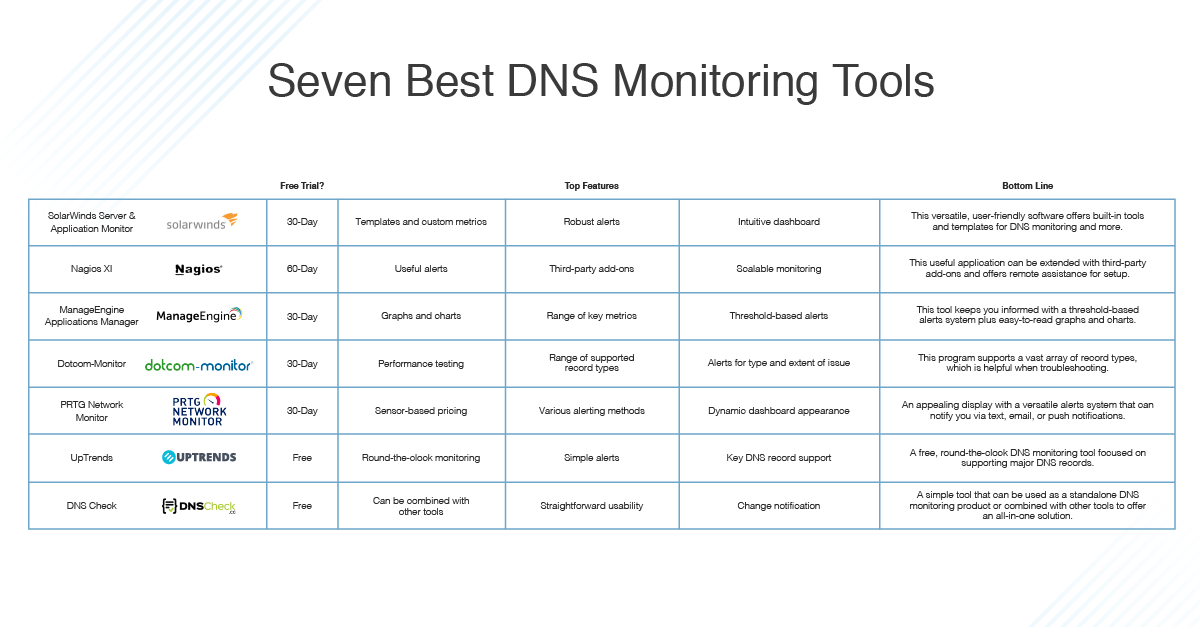
Detect DNS Tunneling done by tools such as iodine with ELK stack + Packetbeat and Watcher : r/netsec
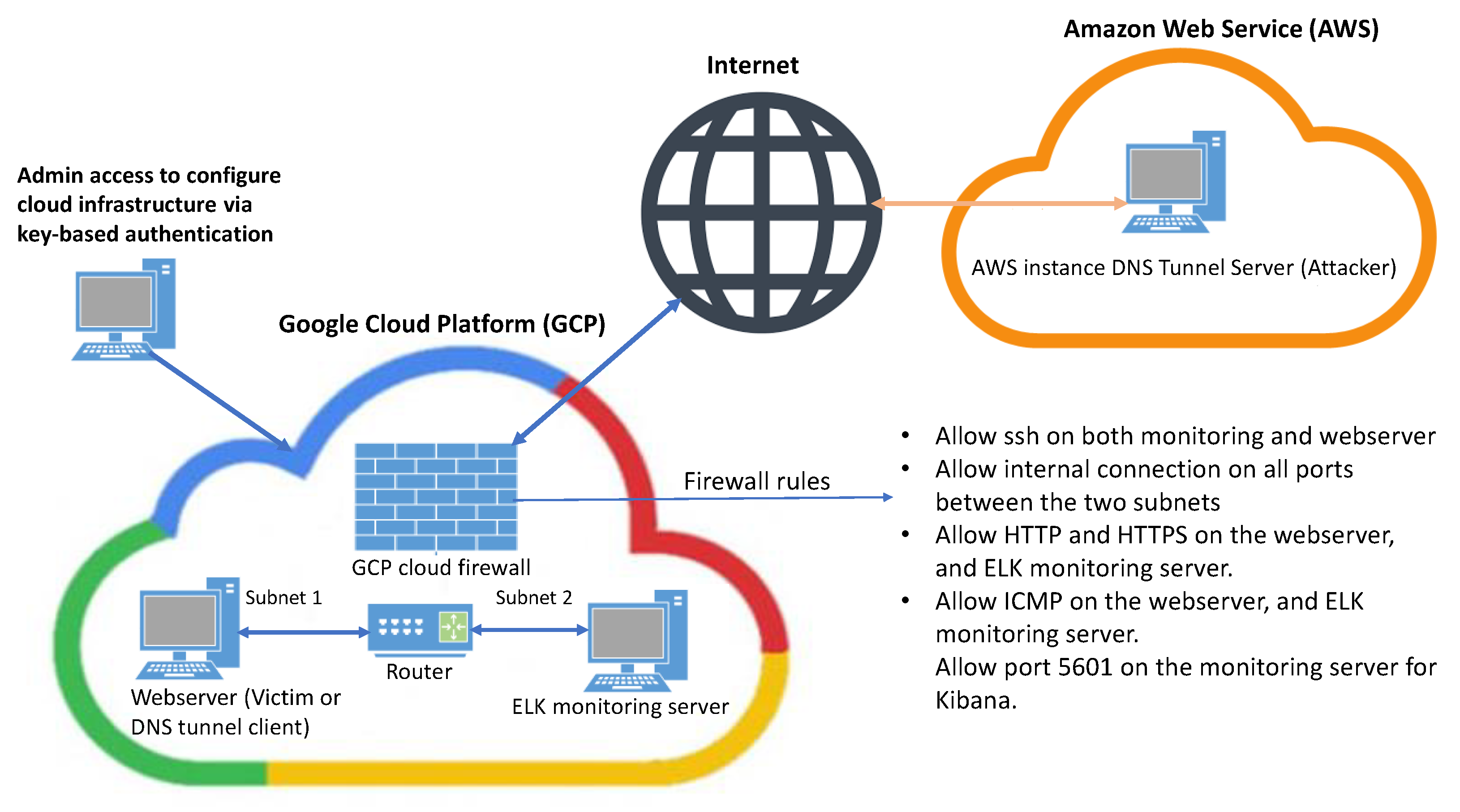
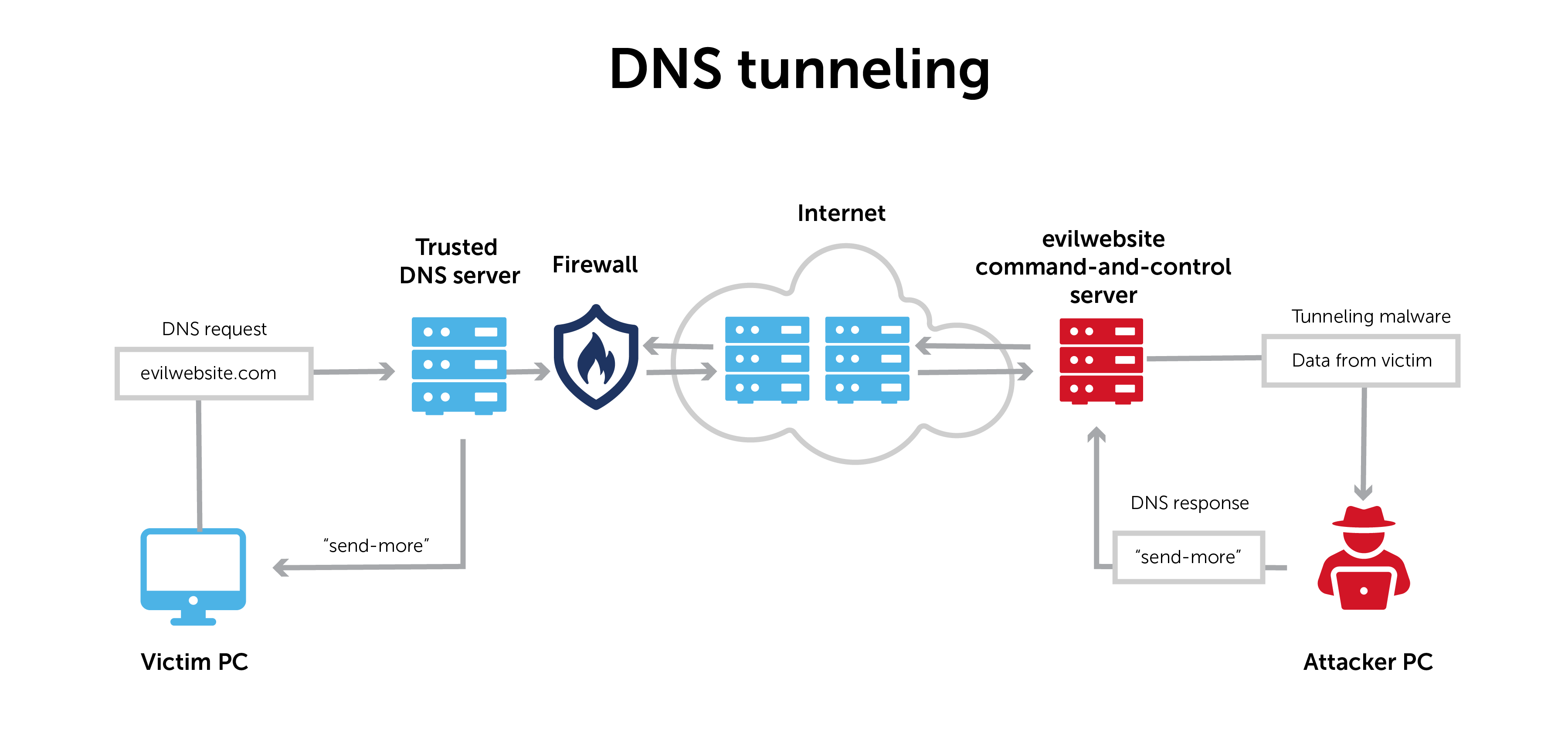
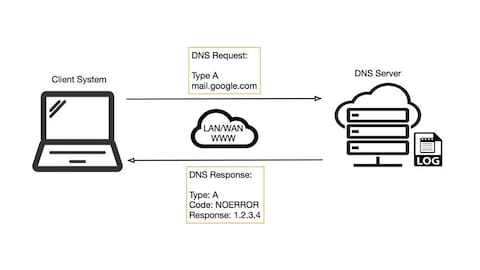
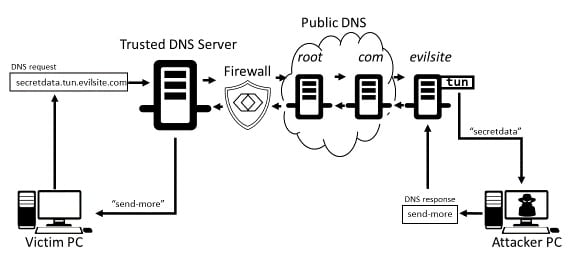
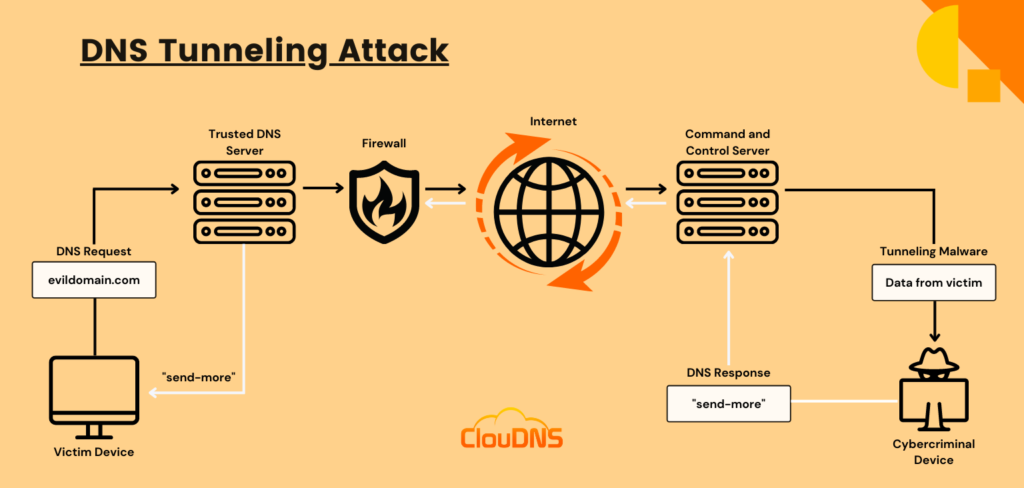
Learn how easy is to bypass firewalls using DNS tunneling (and also how to block it) | by Roger Galobardes | Medium
GitHub - Octoberfest7/DNS_Tunneling: DNS Tunneling using powershell to download and execute a payload. Works in CLM.




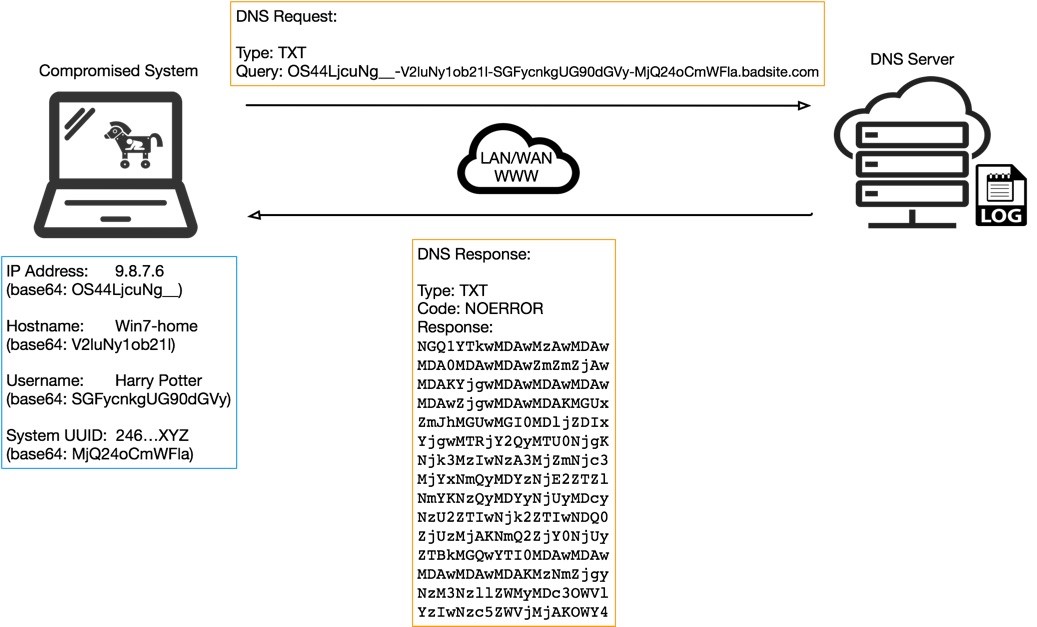
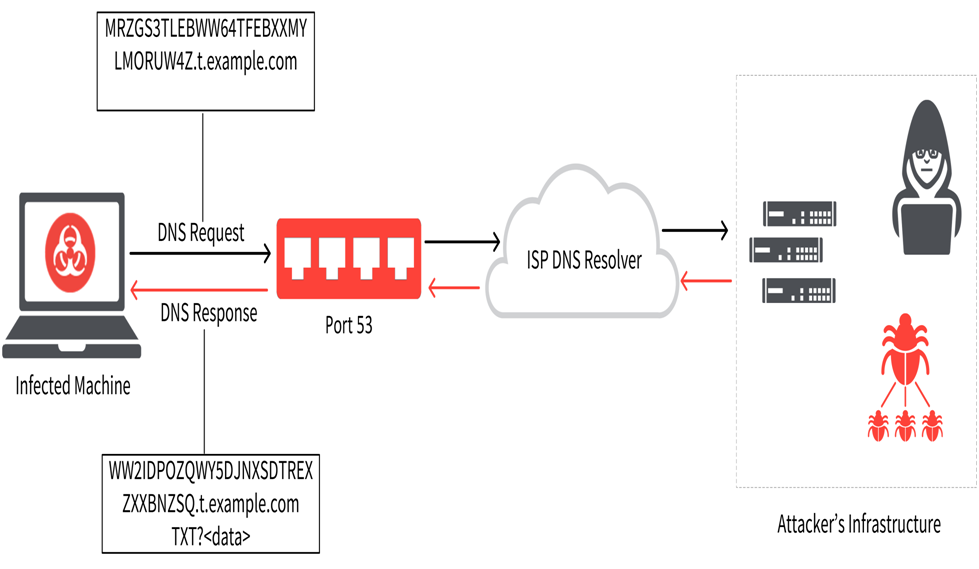
![PDF] Performance assessment and analysis of DNS tunneling tools | Semantic Scholar PDF] Performance assessment and analysis of DNS tunneling tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/7f3bc9a13f911b1e2d1d981fc5c83c5fcf62d2fd/6-Figure2-1.png)